The DDoS attack surge that began last week against Ukrainian government agencies and banks was a bad sign. I was actually preparing a post and wondering if it was appropriate to call out Russia as, at that point, there was no formal attribution.
But c’mon.
Russia’s history of using cyber attacks in conjunction with physical warfare is long and storied. For example, in July 2008, the Republic of Georgia experienced a massive DDoS attack just weeks before Russia launched its military invasion of the country.
And now, as we watched tanks roll and rockets fly into Ukraine yesterday, I don’t think anyone doubts who was behind the cyber attacks, then or now. The new strain of wiper malware unleashed on Ukrainian targets and the ongoing DDoS attacks are clearly just another military front—even if proving it is difficult.
Frankly, I’m worried. Russia has a full quiver of options if it decides to come after critical infrastructure in the West, and we are vulnerable to one of their favorites.
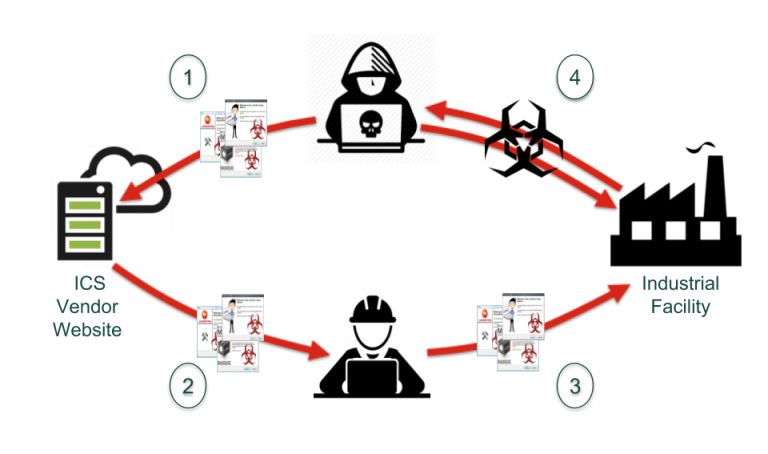
What has changed since the 2008 Georgia invasion is that Russia has become far more active and proficient in both software supply chain attacks and OT-focused attacks. These are likely to be the next wave in any coordinated cyber/military offensive by Russia.
Any country or company with commercial or political connections to Ukraine needs to be prepared for Russian cyber aggression using the software supply chain. The only defense against these attacks is for companies and governments to have a global view of their software supply chain. In other words, they must be able to see—in real time—not only who they buy software from but also what 3rd, 4th, and 5th-party developers have software buried inside the products they use. And they need to be able to locate high-risk software components in minutes.
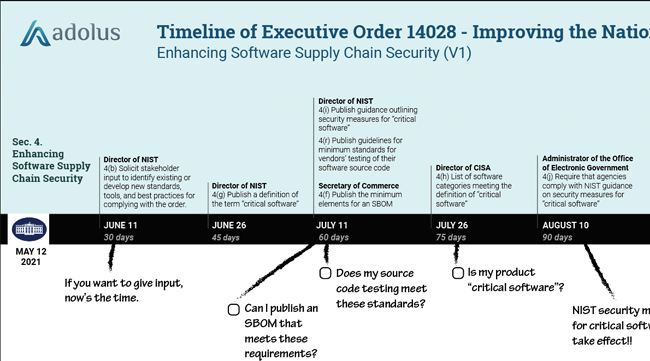
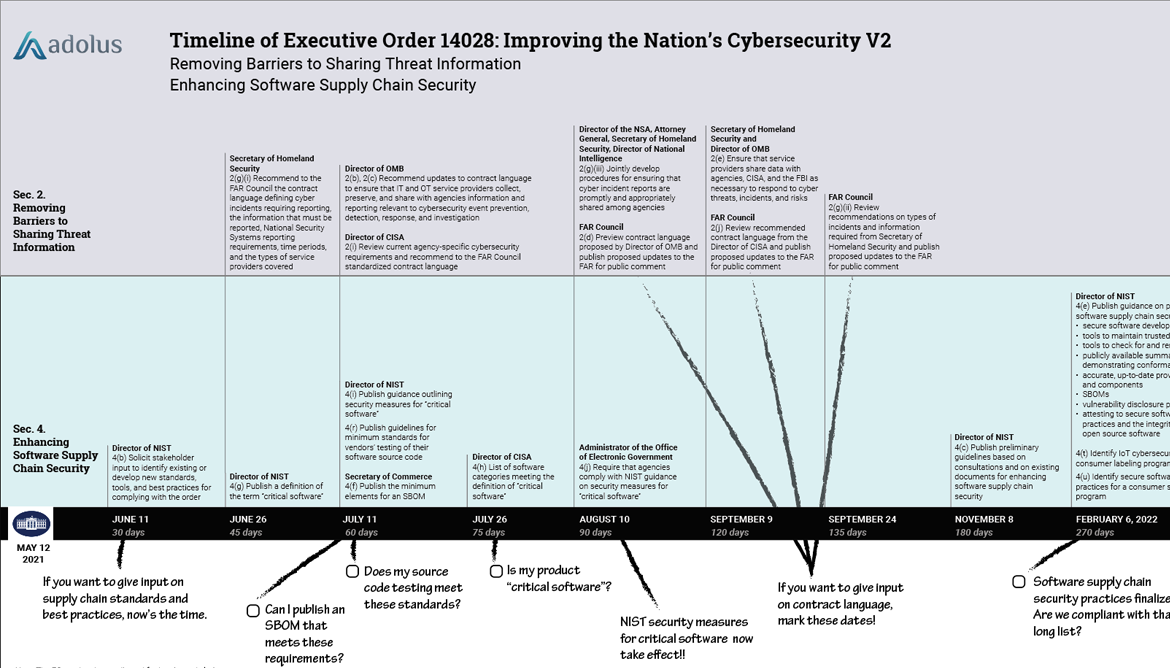
The Software Bill of Materials (SBOM) mandate by the US Government was a critical first step, but you then need a platform for converting the mountains of data inside SBOMs into actionable business intelligence.
And that’s what our team here at aDolus has built. Our FACT platform uses AI, machine learning, and a massive database of OT files and artifacts to make millions and millions of real-time correlations between vendors, products, components, vulnerabilities, and malware. We can find dangerous, untrustworthy files quickly, before they spread across critical infrastructure.
Make no mistake: Putin’s bench of Russian cyber criminals is deep, experienced, and well-funded. He’s done little to restrain them in the past, and now, with the stakes so high, he has every reason to unleash them on western critical infrastructure if he feels provoked.
Platforms like FACT, as well as SBOMs and VEX documents will make the difference between an extended critical system outage (like we saw at Colonial Pipeline) and a rapid and successful defense.
Contact us if you are looking for a fast way to secure your software supply chain.

Eric Byres
Eric is widely recognized as one of the world’s leading experts in the field of OT, IT and IoT software supply chain security. He is the inventor of the Tofino Security technology – the most widely deployed OT-specific firewall in the world. When not setting the product vision, or speaking at a conference, Eric can be found cranking away on his gravel bike.
Stay up to date
Browse Posts
- May 2024
- February 2024
- December 2023
- October 2023
- April 2023
- March 2023
- February 2023
- October 2022
- April 2022
- February 2022
- December 2021
- November 2021
- August 2021
- July 2021
- June 2021
- May 2021
- February 2021
- January 2021
- December 2020
- September 2020
- August 2020
- July 2020
- May 2020
- April 2020
- January 2020
- October 2019
- September 2019
- November 2018
- September 2018
- May 2018
Browse by topics
- Supply Chain Management (16)
- SBOM (15)
- Vulnerability Tracking (15)
- #supplychainsecurity (10)
- Regulatory Requirements (10)
- VEX (8)
- EO14028 (6)
- ICS/IoT Upgrade Management (6)
- malware (6)
- ICS (5)
- vulnerability disclosure (5)
- 3rd Party Components (4)
- Partnership (4)
- Press-release (4)
- #S4 (3)
- Software Validation (3)
- hacking (3)
- industrial control system (3)
- Code Signing (2)
- Legislation (2)
- chain of trust (2)
- #nvbc2020 (1)
- DoD CMMC (1)
- Dragonfly (1)
- Havex (1)
- Log4Shell (1)
- Log4j (1)
- Trojan (1)
- USB (1)
- Uncategorized (1)
- energy (1)
- medical (1)
- password strength (1)
- pharmaceutical (1)














Post a comment