- Blog
- /
- Topic
S4
- All
- Supply Chain Management
- SBOM
- Vulnerability Tracking
- #supplychainsecurity
- Regulatory Requirements
- VEX
- EO14028
- ICS/IoT Upgrade Management
- malware
- ICS
- vulnerability disclosure
- 3rd Party Components
- Partnership
- Press-release
- #S4
- Software Validation
- hacking
- industrial control system
- Code Signing
- Legislation
- chain of trust
- #nvbc2020
- DoD CMMC
- Dragonfly
- Havex
- Log4Shell
- Log4j
- Trojan
- USB
- Uncategorized
- energy
- medical
- password strength
- pharmaceutical
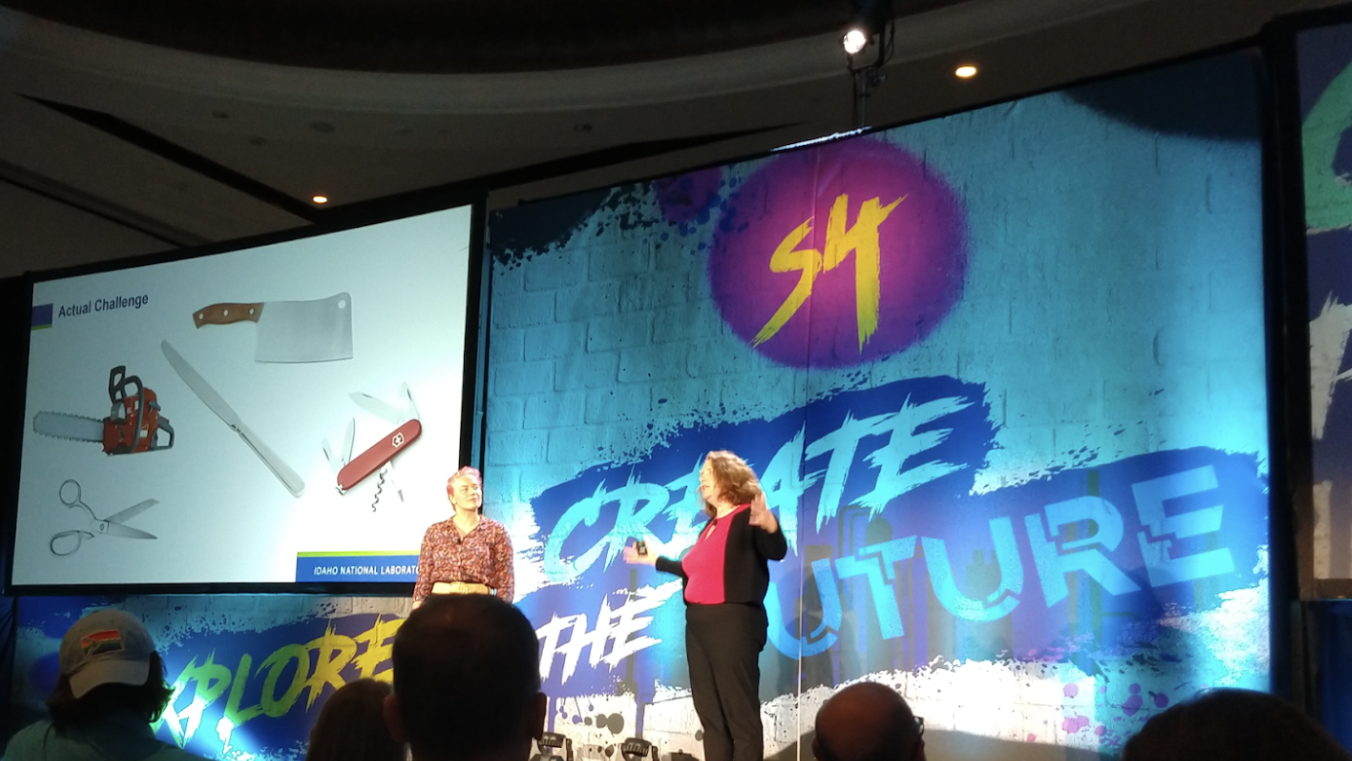
S4x23 SBOM Challenge — Part 3: VEX Document Ingestion
By
Derek Kruszewski on March 16, 2023
Three weeks ago I reported on the first part of the S4x23 SBOM Challenge run by Idaho National Laboratory (INL), which focused on SBOM Creation. Last week I reported on the second part:...
Continue ReadingS4x23 SBOM Challenge — Part 2: SBOM Ingestion
By
Derek Kruszewski on March 8, 2023
Two weeks ago I reported on the first part of the SBOM Challenge at the S4x23 cybersecurity conference in Miami, Florida. The Day 1 goal was for each team to create an accurate SBOM for...
Continue ReadingS4x23 SBOM Challenge — Part 1
By
Derek Kruszewski on February 24, 2023
The aDolus Team has just returned from participating in the SBOM Challenge at the S4x23 cybersecurity conference in Miami, Florida. This blog is the first of a series reporting on what we...
Continue Reading
Loading more posts
No more posts to load
Stay up to date
Browse Posts
Popular
Recent
Archive
- May 2024
- February 2024
- December 2023
- October 2023
- April 2023
- March 2023
- February 2023
- October 2022
- April 2022
- February 2022
- December 2021
- November 2021
- August 2021
- July 2021
- June 2021
- May 2021
- February 2021
- January 2021
- December 2020
- September 2020
- August 2020
- July 2020
- May 2020
- April 2020
- January 2020
- October 2019
- September 2019
- November 2018
- September 2018
- May 2018
Browse by topics
- Supply Chain Management (16)
- SBOM (15)
- Vulnerability Tracking (15)
- #supplychainsecurity (10)
- Regulatory Requirements (10)
- VEX (8)
- EO14028 (6)
- ICS/IoT Upgrade Management (6)
- malware (6)
- ICS (5)
- vulnerability disclosure (5)
- 3rd Party Components (4)
- Partnership (4)
- Press-release (4)
- #S4 (3)
- Software Validation (3)
- hacking (3)
- industrial control system (3)
- Code Signing (2)
- Legislation (2)
- chain of trust (2)
- #nvbc2020 (1)
- DoD CMMC (1)
- Dragonfly (1)
- Havex (1)
- Log4Shell (1)
- Log4j (1)
- Trojan (1)
- USB (1)
- Uncategorized (1)
- energy (1)
- medical (1)
- password strength (1)
- pharmaceutical (1)
Sidebar