- Blog
- /
- Author
Ron Brash
Ron Brash is a household name in ICS/OT cybersecurity and embedded vulnerability research and an honored recipient of Plant Engineering’s Top 40 under 40 award. Ron leads aDolus’ technical research, integrations, DIY home projects, and death-defying watersport shenanigans.

Log4j: Panic or Lesson? | How to Protect Deployed Assets
By
Ron Brash on December 21, 2021
Cleaning up the Mess will Take a Methodical Approach Nearly every week the cybersecurity community buzzes around a newly discovered vulnerability or a breach. December’s alert for the ...
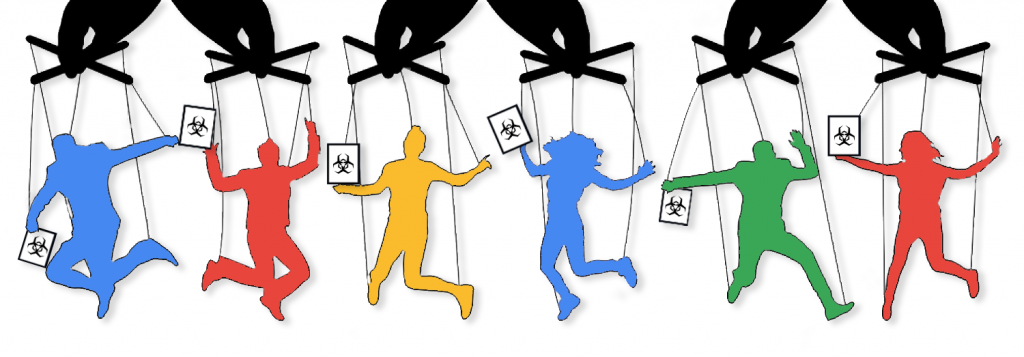
Continue ReadingDon’t Judge an Ebook by Its Cover
By
Ron Brash on May 12, 2020
Interesting times lead to interesting opportunities. The current pandemic is proving no exception, but, sadly, it’s an opportunity for some attackers who have laid a rather cunning trap. As...
Continue Reading
Loading more posts
No more posts to load
Stay up to date
Browse Posts
Popular
Recent
Archive
- May 2024
- February 2024
- December 2023
- October 2023
- April 2023
- March 2023
- February 2023
- October 2022
- April 2022
- February 2022
- December 2021
- November 2021
- August 2021
- July 2021
- June 2021
- May 2021
- February 2021
- January 2021
- December 2020
- September 2020
- August 2020
- July 2020
- May 2020
- April 2020
- January 2020
- October 2019
- September 2019
- November 2018
- September 2018
- May 2018
Browse by topics
- Supply Chain Management (16)
- SBOM (15)
- Vulnerability Tracking (15)
- #supplychainsecurity (10)
- Regulatory Requirements (10)
- VEX (8)
- EO14028 (6)
- ICS/IoT Upgrade Management (6)
- malware (6)
- ICS (5)
- vulnerability disclosure (5)
- 3rd Party Components (4)
- Partnership (4)
- Press-release (4)
- #S4 (3)
- Software Validation (3)
- hacking (3)
- industrial control system (3)
- Code Signing (2)
- Legislation (2)
- chain of trust (2)
- #nvbc2020 (1)
- DoD CMMC (1)
- Dragonfly (1)
- Havex (1)
- Log4Shell (1)
- Log4j (1)
- Trojan (1)
- USB (1)
- Uncategorized (1)
- energy (1)
- medical (1)
- password strength (1)
- pharmaceutical (1)
Sidebar