Today, reporters Betsy Woodruff Swan and Eric Geller at Politico published a story: “BlackBerry resisted announcing major flaw in software powering cars, hospital equipment.” They outline how BlackBerry willfully hid the fact that their key operating system QNX contained a collection of vulnerabilities (originally discovered and named BadAlloc by Microsoft). It seems other companies affected by BadAlloc announced the issue way back in May. Not so BlackBerry; instead they followed a deny–obstruct–surrender playbook, presumably to protect their reputation (I wonder how that’s working out) and their bottom line (I guess we’ll see).
These guys are the poster child for why we need SBOMs, especially for critical infrastructure.
If you’re not familiar with QNX, it powers critical embedded systems across many industries, from Autonomous Vehicles, Aerospace & Defense systems, and Industrial Control Systems to Robotics & Automation. It is deeply and widely present in OT environments.
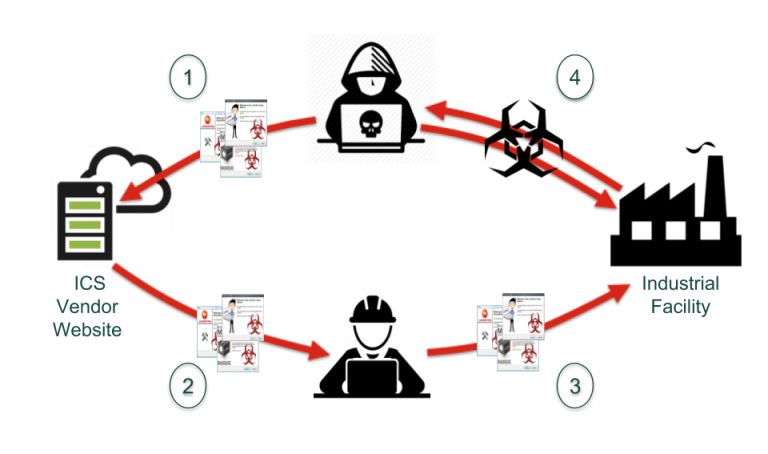
Initially, BlackBerry argued with CISA that QNX was unaffected by the vulnerabilities. But CISA informed them otherwise. Politico reports that BlackBerry then declined to make any public acknowledgement of the vulnerabilities, preferring instead to contact their customers directly. The problem is, BlackBerry only kept track of their direct customers and didn’t appreciate their role as a link in the supply chain. All the OEMs that embedded QNX in their products along with their customers, who went on to sell their own products (and so on and so on), were unaware they were harbouring the vulnerabilities.
From the article:
When companies such as BlackBerry sell their software to equipment manufacturers, they rarely provide detailed records of the code that goes into the software — leaving hardware makers, their customers and the government in the dark about where the biggest risks lie.
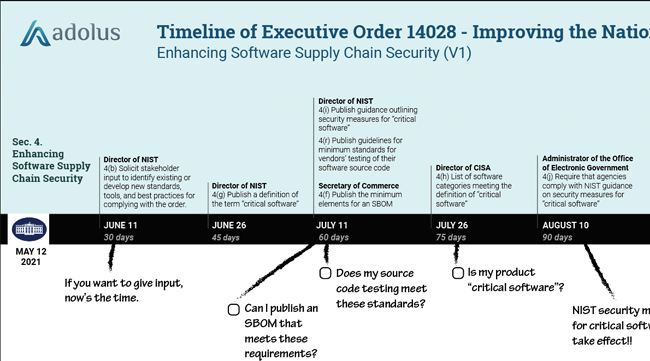
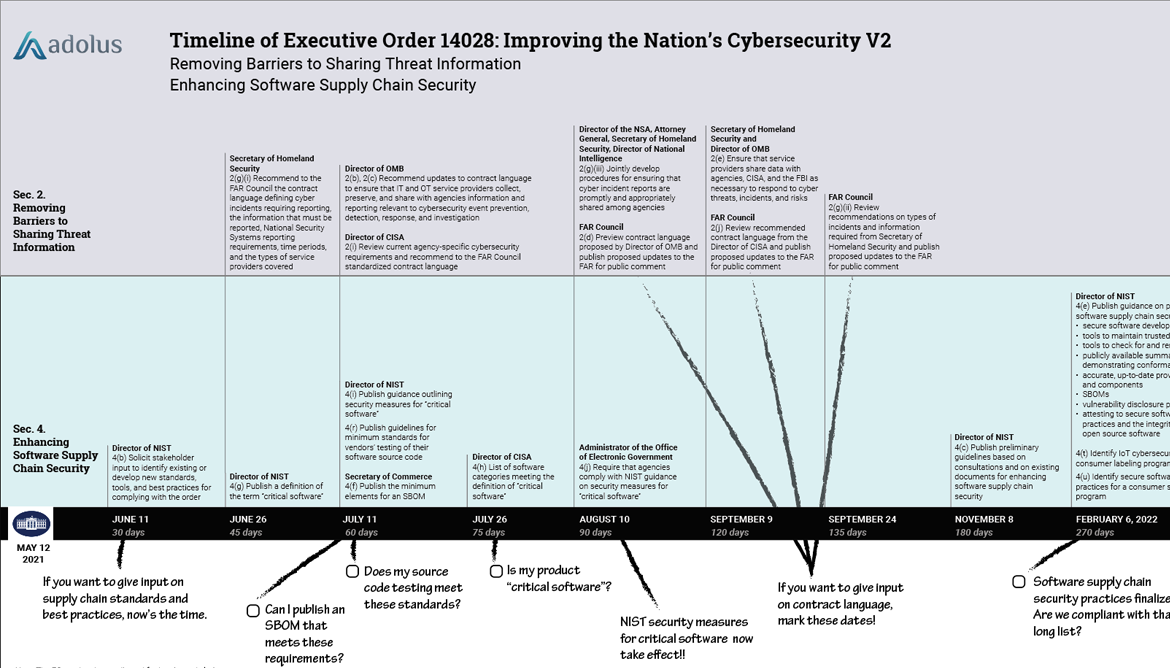
The Executive Order we’ve been writing about aims to end this situation with the provisioning of SBOMs. If BlackBerry had provided an SBOM to their OEM customers, they would be properly informed about the risks and they would have been in a position to share that information with their customers. The federal government has frequently referred to their cybersecurity policies requiring a "whole-nation-effort" but that requires good faith participation. BlackBerry can't just furtively whisper in the ears of a few customers and hope no one else notices.
One other troubling consequence of BlackBerry’s behaviour is the potential impact this stance could have on SBOM-related initiatives, such as VEX. One of the concerns about SBOMs is that they can trigger a tidal wave of vulnerability alerts that’s paralyzing. VEX provides vendors with the capability to identify which vulnerabilities are actually exploitable in their products (since most of them aren’t) to get the list down to priority vulnerabilities that need attention. But VEX relies on transparency from vendors. If a company is trying to be sneaky, all they’ll do is produce misleading documents that add to rather than reduce supply chain risk.
Since BlackBerry doesn't seem to want to do the right thing and warn QNX users that their critical devices have a major vulnerability, we plan to do the work for them. We are currently scanning through our SBOM database of millions of OT files looking for the offending firmware. We will then provide private notifications to our customers. If you want to be on that notification list (and have a valid reason to be on it), contact us:

Eric Byres
Eric is widely recognized as one of the world’s leading experts in the field of OT, IT and IoT software supply chain security. He is the inventor of the Tofino Security technology – the most widely deployed OT-specific firewall in the world. When not setting the product vision, or speaking at a conference, Eric can be found cranking away on his gravel bike.
Stay up to date
Browse Posts
- May 2024
- February 2024
- December 2023
- October 2023
- April 2023
- March 2023
- February 2023
- October 2022
- April 2022
- February 2022
- December 2021
- November 2021
- August 2021
- July 2021
- June 2021
- May 2021
- February 2021
- January 2021
- December 2020
- September 2020
- August 2020
- July 2020
- May 2020
- April 2020
- January 2020
- October 2019
- September 2019
- November 2018
- September 2018
- May 2018
Browse by topics
- Supply Chain Management (16)
- SBOM (15)
- Vulnerability Tracking (15)
- #supplychainsecurity (10)
- Regulatory Requirements (10)
- VEX (8)
- EO14028 (6)
- ICS/IoT Upgrade Management (6)
- malware (6)
- ICS (5)
- vulnerability disclosure (5)
- 3rd Party Components (4)
- Partnership (4)
- Press-release (4)
- #S4 (3)
- Software Validation (3)
- hacking (3)
- industrial control system (3)
- Code Signing (2)
- Legislation (2)
- chain of trust (2)
- #nvbc2020 (1)
- DoD CMMC (1)
- Dragonfly (1)
- Havex (1)
- Log4Shell (1)
- Log4j (1)
- Trojan (1)
- USB (1)
- Uncategorized (1)
- energy (1)
- medical (1)
- password strength (1)
- pharmaceutical (1)














Post a comment