Wrapping up my year on December 31, I was delighted to join ICS cybersecurity luminary Dale Peterson for his December: ICS Security Month in Review episode of the Unsolicited Response Podcast. Dale was kind enough to invite me on to discuss the big stories of December 2020 and to throw out some predictions on what’s in store for us in 2021. Here I’ll present a quick teaser of our discussion; I encourage you to listen to the full podcast.
Not surprisingly, we started with the SolarWinds attacks. Before the holidays I wrote a blog about some important takeaways from SolarWinds and it was great to hear Dale’s thoughts on the subject. We didn’t do a technical deep dive on the topic — others have already done a great job on that — but we did take a 10,000 ft perspective on what needs to change in the industry to protect control systems from these kinds of supply chain attacks. I strongly believe we need to see better, more sophisticated information sharing between ICS vendors and asset owners. (Reading through hundreds of vendor-supplied PDFs to review vulnerability notices is a gong show of inefficiency!)
The SolarWinds situation proves that vendors cannot shirk the responsibility of protecting their customers from hijacked code. Just take a look at their stock price. (I’ll be publishing more on this next week.) Dale and I are also in agreement that this information sharing is better provided by a commercial, paid service than by some government-sponsored effort.
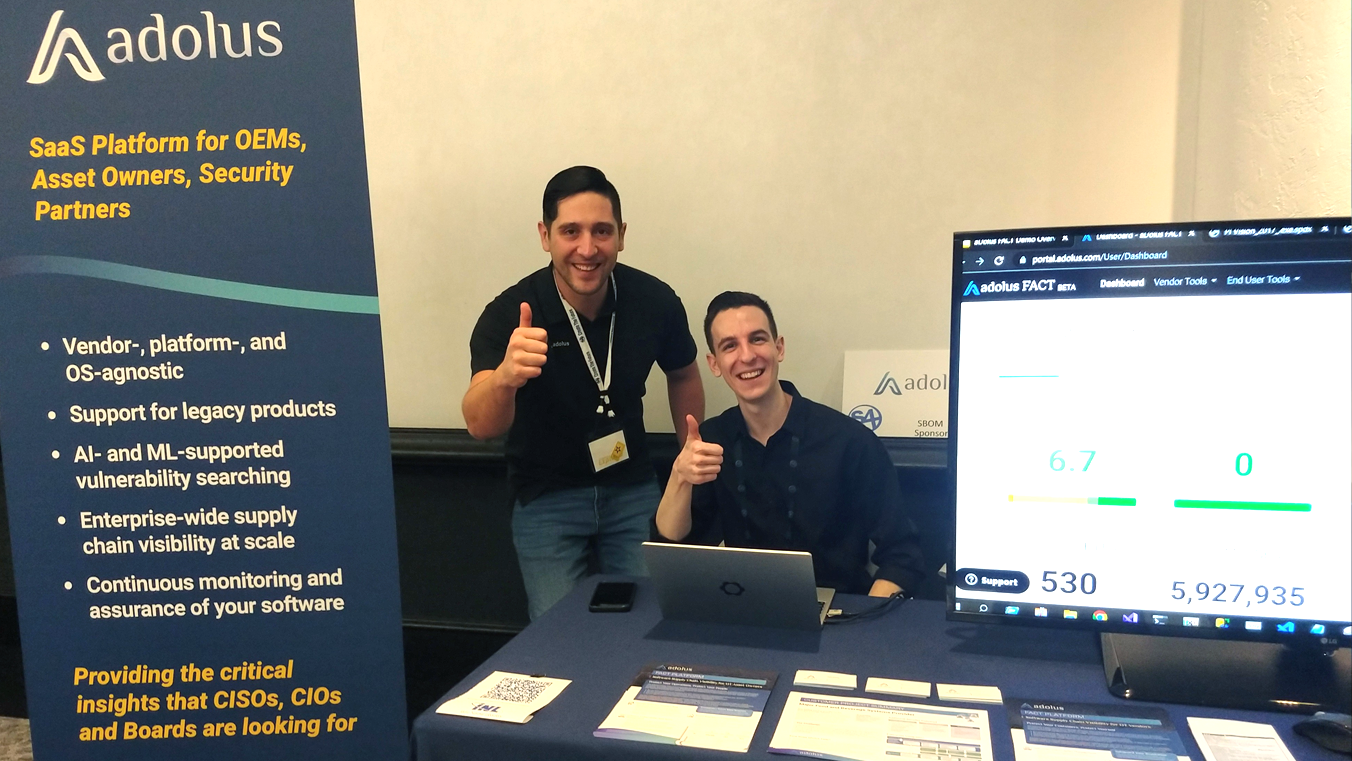
I had several other takeaways on the subject (the limitations of code signing, SBOMs, etc.) and Dale had some thoughts on potential business models for an information-sharing service — that is, who pays for it? We’ve found here at aDolus that vendors have been signing up with us more often than the asset owners.
Next, we talked about the recent Dragos $110M funding round. Back in my Tofino days, hearing a number like that would have knocked me off my bike. Dale reckoned this shows that venture capitalists out there are envisioning multi-billion dollar cybersecurity companies serving the OT market. I agree to a point, but I see these companies getting swallowed up by the likes of Google or Cisco by the time they hit $1B. I may be burned at the stake by my ICS friends for this, but eventually IT and OT security will be one big market. I predict we’ll be seeing lots of M&A activity in ICS security over the next few years.
We also talked about how few ICS incidents occurred in 2020 and how inconsequential they were. My thoughts are that cyber hacking has become a profession — and professionals go where the money is (or the politics); right now there’s more profit in ransomware and better ROI on the IT side. That said, the majority of the ICS-focused attacks we’ve seen in the last decade have been quiet infiltrations with the attackers staying under the radar and biding their time. So perhaps there were attacks in 2020... and we just haven’t seen them yet.
Finally, Dale and I moved on to Wins, Fails, and Predictions… but you’ll have to listen to the full podcast for those. :-)
Happy New Year everyone!

Eric Byres
Eric is widely recognized as one of the world’s leading experts in the field of OT, IT and IoT software supply chain security. He is the inventor of the Tofino Security technology – the most widely deployed OT-specific firewall in the world. When not setting the product vision, or speaking at a conference, Eric can be found cranking away on his gravel bike.
Stay up to date
Browse Posts
- May 2024
- February 2024
- December 2023
- October 2023
- April 2023
- March 2023
- February 2023
- October 2022
- April 2022
- February 2022
- December 2021
- November 2021
- August 2021
- July 2021
- June 2021
- May 2021
- February 2021
- January 2021
- December 2020
- September 2020
- August 2020
- July 2020
- May 2020
- April 2020
- January 2020
- October 2019
- September 2019
- November 2018
- September 2018
- May 2018
Browse by topics
- Supply Chain Management (16)
- SBOM (15)
- Vulnerability Tracking (15)
- #supplychainsecurity (10)
- Regulatory Requirements (10)
- VEX (8)
- EO14028 (6)
- ICS/IoT Upgrade Management (6)
- malware (6)
- ICS (5)
- vulnerability disclosure (5)
- 3rd Party Components (4)
- Partnership (4)
- Press-release (4)
- #S4 (3)
- Software Validation (3)
- hacking (3)
- industrial control system (3)
- Code Signing (2)
- Legislation (2)
- chain of trust (2)
- #nvbc2020 (1)
- DoD CMMC (1)
- Dragonfly (1)
- Havex (1)
- Log4Shell (1)
- Log4j (1)
- Trojan (1)
- USB (1)
- Uncategorized (1)
- energy (1)
- medical (1)
- password strength (1)
- pharmaceutical (1)


















Post a comment