So you don’t sell to the Feds…
Today’s blog is going to take a break from analyzing a specific section of the Executive Order on Improving the Nation’s Cybersecurity and focus on who will be impacted by the order.
I got thinking about this last week when Tom Clary posted this insightful comment on LinkedIn:
At one level Tom is right. As Robert Chesney and Trey Herr pointed out in their blog on the EO:[This] Executive Order in no way compels private sector critical infrastructure to do anything different. It seems intended to better protect and secure federal government and agency information systems and data. So its real impact, via new guidelines to come, will be on the vendors who sell into federal agencies.
EOs are not statutes… Presidents can’t just make rules that the private sector must obey; that’s Congress’s job.
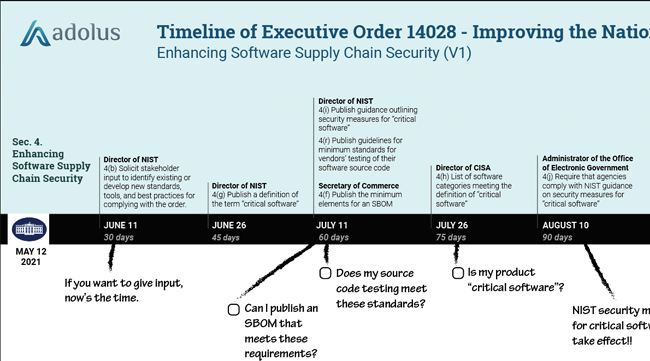
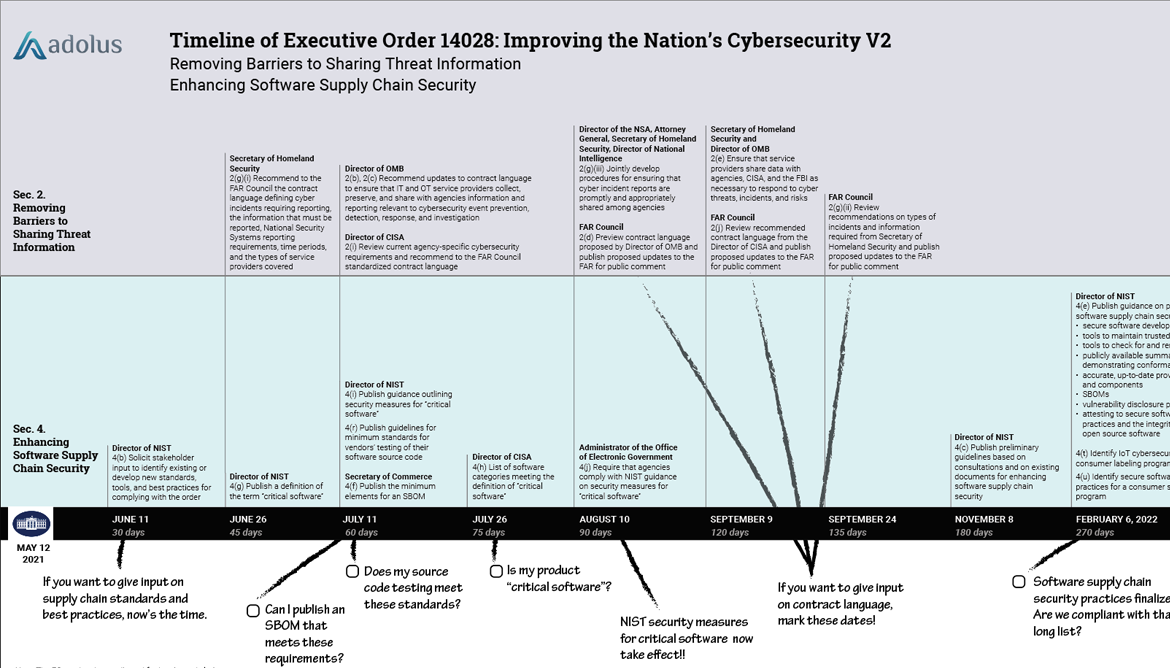
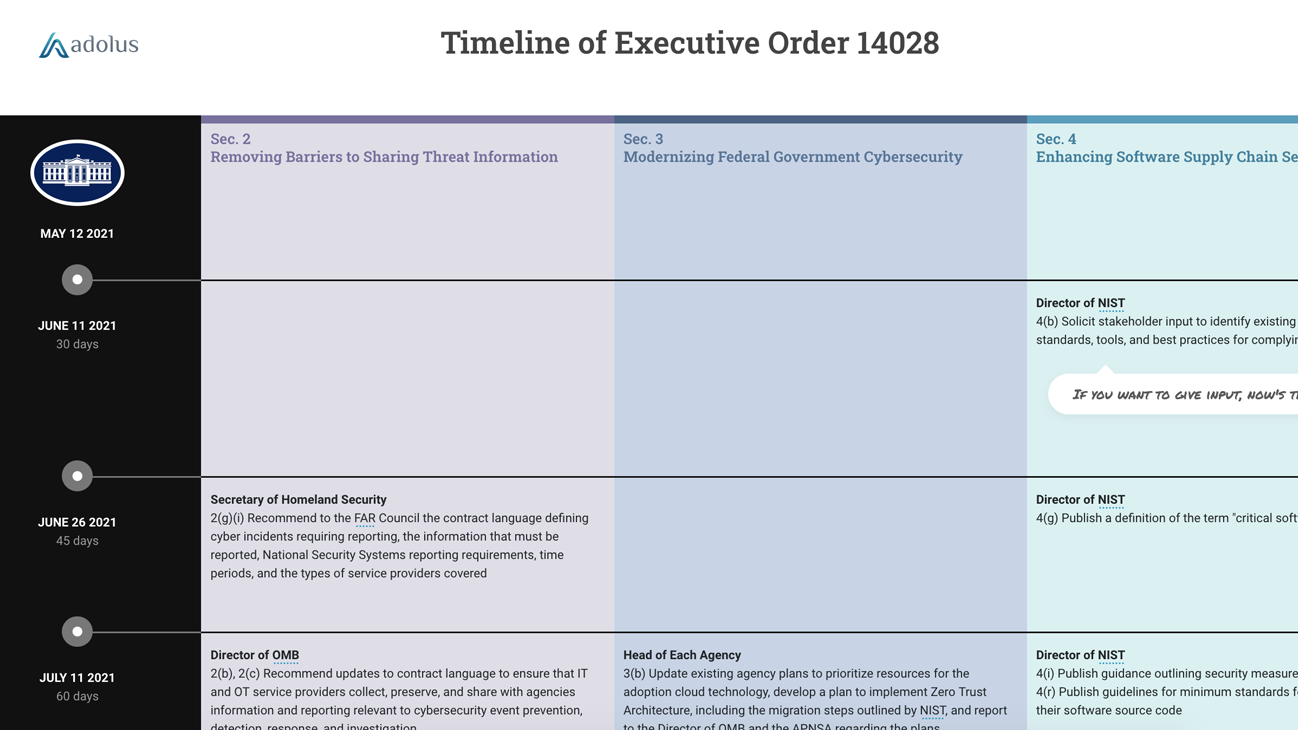
Instead, Executive Orders can have the effect of law, ordering federal entities to take specific actions. They can also require certain terms to be included in federal contracts. And this is where the rubber hits the road in this EO for both the IT and OT industries.
The impact of US government contracts on the IT industry is pretty obvious; we all know that the US Government buys a lot of IT technology and services, and that gives them clout. Clauses seen in government IT contracts tend to show up in corporate IT contracts fairly quickly.
But what about OT contracts — will this EO influence those? We tend to think of OT deployments in terms of the private sector, but the US Defence department buys a lot of ICS equipment to keep the water flowing and the lights on at its military bases around the world. Ships and planes use OT products. And government bodies like the US Army Corp of Engineers and the Tennessee Valley Authority buy lots of OT. So the US Federal government is a significant purchaser of OT products for both civilian and defence projects.
This OT “procurement power” will significantly impact behavior outside the government. First if supplier X agrees to provide SBOMs to the US government, finding a reason to refuse to provide SBOMs to its large commercial clients will be a struggle. This will ripple far beyond the US. We’ve become aware of sovereign oil companies in the Middle East who are now looking to duplicate the requirements for the Software Supply Chain for all OT purchases they make in the next year.
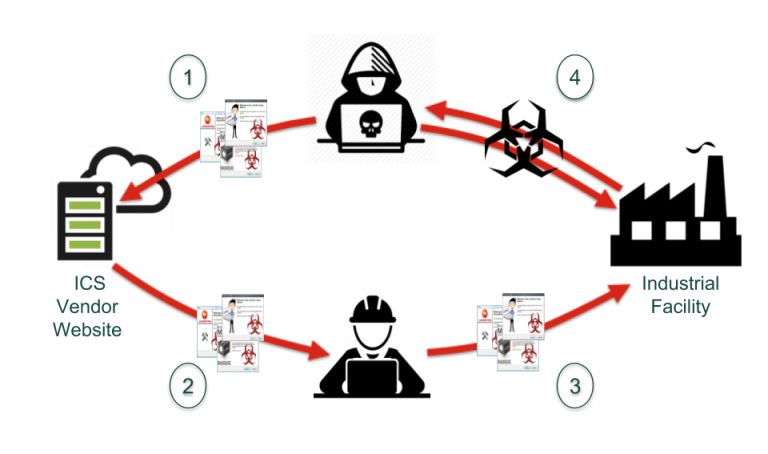
The second reason to expect that the EO will impact companies who don’t have direct sales to the US government is the EO’s focus on the software supply chain. The supply chain is called a chain for a reason. Even if you don't sell directly to the federal government, what if one of your customers does, and they use your product as part of a larger solution? If the Feds cancel their contract for non-compliance, you can say goodbye to that customer.
Finally, Section 2 of the EO may have a very broad-reaching impact on the general market. As I noted in my previous blog post, the stated goal of Section 2 is the sharing of incident data; however, some language in the section is considerably broader. Section 2(e) refers to the information necessary for the government to respond to cyber threats, incidents, and risks. This would include a wide range of security information and may implicate companies that sell cybersecurity data to the federal government. Companies in the OT threat intelligence business will need to watch this closely.
So while cybersecurity legislation (rather than an EO) could have had a more direct impact on the private sector and the OT market, it would be a mistake to think that this EO will make little difference to the OT world. The EO will influence information sharing, contacting, and purchasing behavior worldwide. As well, this EO is likely to act as a model for how Congress might bolster security in the nation’s critical infrastructures. Finally, it will definitely inform industry regulations like NERC CIP-013.
So even if your company doesn’t sell to the US Government, you need to start preparing as if you do. You might just discover you are a key link in the chain.
If you want to be notified of the next report on EO14028, click Subscribe (down to the right).

Eric Byres
Eric is widely recognized as one of the world’s leading experts in the field of OT, IT and IoT software supply chain security. He is the inventor of the Tofino Security technology – the most widely deployed OT-specific firewall in the world. When not setting the product vision, or speaking at a conference, Eric can be found cranking away on his gravel bike.
Stay up to date
Browse Posts
- May 2024
- February 2024
- December 2023
- October 2023
- April 2023
- March 2023
- February 2023
- October 2022
- April 2022
- February 2022
- December 2021
- November 2021
- August 2021
- July 2021
- June 2021
- May 2021
- February 2021
- January 2021
- December 2020
- September 2020
- August 2020
- July 2020
- May 2020
- April 2020
- January 2020
- October 2019
- September 2019
- November 2018
- September 2018
- May 2018
Browse by topics
- Supply Chain Management (16)
- SBOM (15)
- Vulnerability Tracking (15)
- #supplychainsecurity (10)
- Regulatory Requirements (10)
- VEX (8)
- EO14028 (6)
- ICS/IoT Upgrade Management (6)
- malware (6)
- ICS (5)
- vulnerability disclosure (5)
- 3rd Party Components (4)
- Partnership (4)
- Press-release (4)
- #S4 (3)
- Software Validation (3)
- hacking (3)
- industrial control system (3)
- Code Signing (2)
- Legislation (2)
- chain of trust (2)
- #nvbc2020 (1)
- DoD CMMC (1)
- Dragonfly (1)
- Havex (1)
- Log4Shell (1)
- Log4j (1)
- Trojan (1)
- USB (1)
- Uncategorized (1)
- energy (1)
- medical (1)
- password strength (1)
- pharmaceutical (1)














Post a comment